Keeping an eye on online identity, privacy, and security.
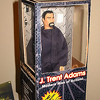
J. Trent Adams
 I am the Director of Ecosystem Security for Proofpoint. My focus is on community-driven development of secure online communications. Prior to that, I filled similar roles for PayPal and the non-profit Internet Society. In general, I build relationships between technologists, developers, and regulators to help them collaborate on trusted online communications. Previously, I was the Founder of MatchMine, Chief Innovator for the Kraft Group Sports Properties, and Executive Producer for the New England Patriots.
I am the Director of Ecosystem Security for Proofpoint. My focus is on community-driven development of secure online communications. Prior to that, I filled similar roles for PayPal and the non-profit Internet Society. In general, I build relationships between technologists, developers, and regulators to help them collaborate on trusted online communications. Previously, I was the Founder of MatchMine, Chief Innovator for the Kraft Group Sports Properties, and Executive Producer for the New England Patriots.
Being in Star Wars: The Force Awakens. [ Video | Photos | Interview | Essay ]